Securing OT Infrastructure: We Can’t Secure What We Don’t See
With the growing trend of connected networks, a key challenge for businesses is to protect the assets that make up their Operational Technology (OT) infrastructure. OT systems are typically more complex and have a longer life cycle than IT systems, making them increasingly prone to cyber attacks. As cyber threats become more sophisticated, companies have to remain vigilant in order to protect these assets.

The importance of protecting OT infrastructure cannot be emphasized enough. OT systems are responsible for critical operations: from manufacturing processes and power plants, to water systems and healthcare networks. Any disruption in these operations can have serious consequences. That’s why it’s essential for businesses to have an effective way of securing OT infrastructure.
The key idea here is: “We can’t secure what we don’t see”. While security measures must be taken, it is not enough for companies to simply put in place firewalls and anti-virus software. These systems, while important, are not designed to detect cyber threats in OT systems. To truly understand the threats out there and protect against them, businesses need to have visibility into their OT systems.
Monitor your OT systems
The best way to get this visibility is to first connect legacy OT assets with modern technology. Companies should look for digital solutions that allow them to monitor their OT systems in real-time, extract useful data from them, and use this data to develop automation capabilities and data-driven decisions. With data from these OT systems, businesses can begin to build up an in-depth understanding of their operational network. This will allow them to detect, isolate, and respond to threats quickly and effectively.
Secure your OT Infrastructure
Companies that are determined to protect their OT systems should start by learning more about the attacks that these systems face. Having an understanding of the threats out there is an essential first step in securing any OT infrastructure. After that, they should look at tools and solutions that can help them monitor their networks in real-time, extract data, and build up automated security measures. Following these steps is essential for any business looking to protect its Operational Technology infrastructure.
Insoft Services has a solution for you
Insoft Services being a partner to Cisco that is truly leading in Cyber Security could recommend a solution to undertake your journey to Secure Industry 4.0.
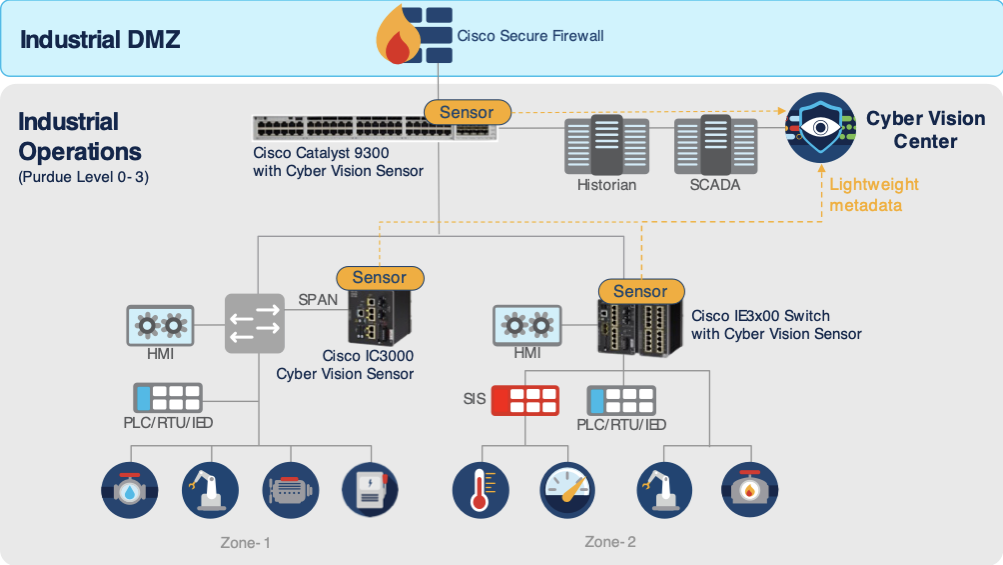
Cisco Cyber Vision provides actionable insights to secure your industrial networks:
- have precise view of your OT asset inventory, communication patterns, network topologies and bring detailed information on OT assets and threats to other security products (NGFW, ISE, StealthWatch)
- create asset groups and together with Cisco ISE (Identity Service Engine) dynamically enforce segmentation policies
- have combined protocol analysis, intrusion detection, behavioral analysis, and OT threat intelligence to detect asset vulnerabilities, and any attack tactic
- unify OT and IT security by adding your OT to your SIEM, SOAR, and XDR platforms.
- extend Cyber Vision’s OT intelligence to your IT applications, with out-of-the-box integrations and a rich API.
Cisco Cyber Vision is made up of network sensors for passively decoding industrial network traffic and sending non-disruptive requests to industrial devices, plus a central platform for data storage, analytics and anomaly detection.
The internal cross-team training of IT and OT teams is imperative for companies to maintain proper cyber security today. As technology penetrates deeply into OT, it is necessary for companies to integrate the latest cyber security measures into their workflow. Cross-team training enables each of these teams to learn from one another and understand the implications of security measures, along with the emergence of new technologies and how it affects security systems. Finally, it allows staying abreast of the ever-changing world of technology and adequately protects their clients and end users.
Overall, IBN offers tremendous potential for organizations, enabling them to maximize agility and efficiency across the network. By utilizing the power of intent-based machine intelligence, the technology promises to usher in a new era of smarter networking.
Download our brochures:
In Insoft Services we highly recommend the following courses:
- INCVDO – Cisco CyberVision Deployment & Operation
- SISE v4.0 – Implementing and Configuring Cisco Identity Services Engine
- SSNGFW – Securing Networks with Cisco Firepower Next-Generation Firewall
- SCOR – Implementing and Operating Cisco Security Core Technologies
- Certified Internet of Things Security Practitioner

 Finland
Finland Germany
Germany Denmark
Denmark Sweden
Sweden Italy
Italy Netherlands
Netherlands Norway
Norway 

































No Comments