Getting Started With FortiGate REST API
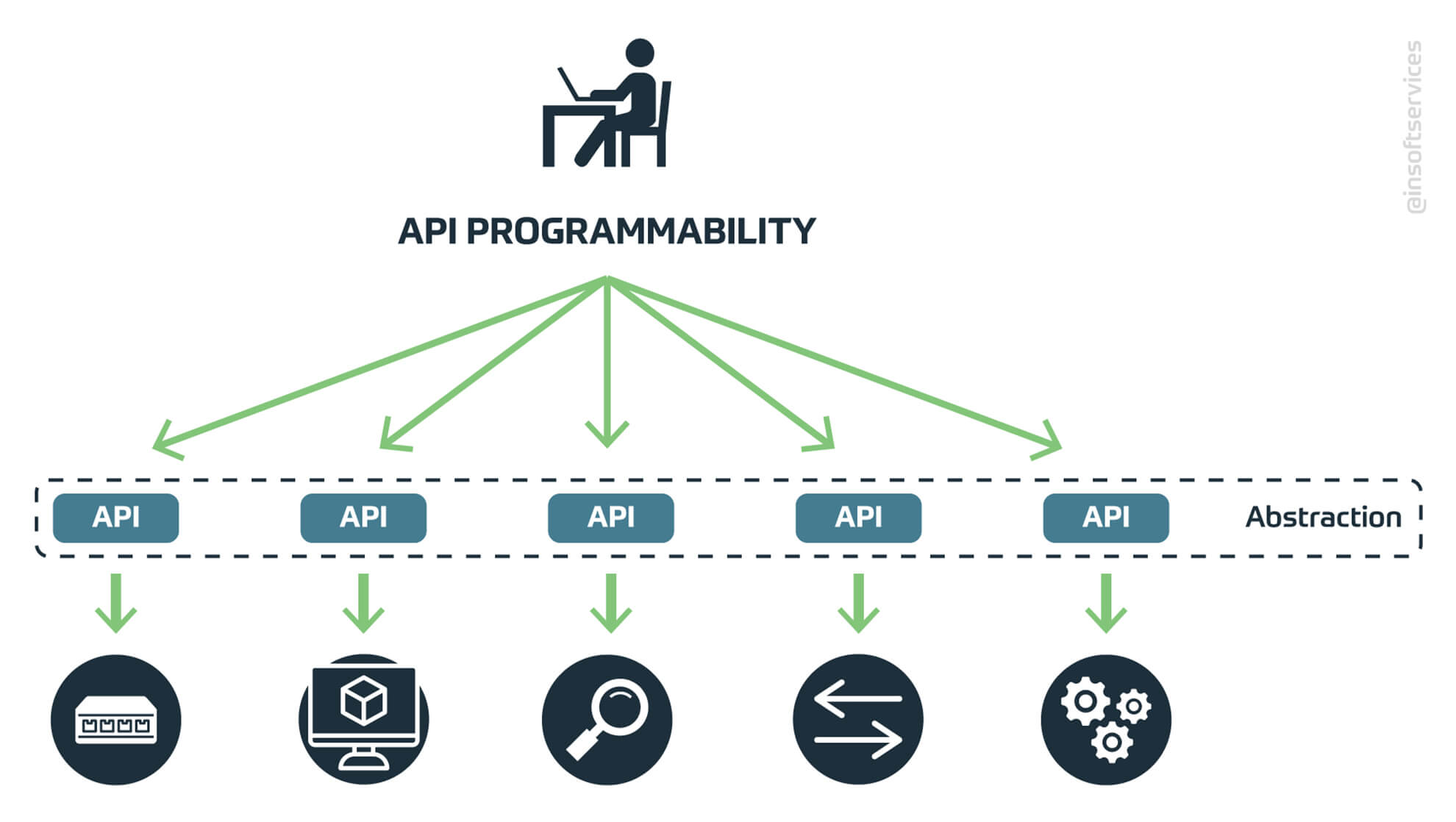
Are you looking to dive into the field of programming your enterprise security infrastructure and automating your security workflows? How to use REST API for network programmability? Curious about the automation options available for the Fortinet security fabric? If your answer is yes, then this FortiOS network programmability series is for you.
Software is eating up the world?
“Software is eating up the world” is a statement that falls out of almost every technologically savvy mouth today, and the network hasn’t been left out. The initial hype around Software Defined Networking is now giving way to real and implementable programmable solutions.
Network vendors are now hitting the market with programmable switches and network controllers such as the Cisco DNA Center. Orchestration tools such as Ansible and Kubernetes are also being used to manage Data Centers and cloud networks at scale. Consequently, security solutions are now being built on extensible platforms that can integrate with other infrastructure through APIs so as to enable quick adaptability to changes in the network.
What is an API?
These are a set of routines, protocols, and tools for building software applications, it dictates how software components should interact and share information with each other.

An API facilitates communication between a client and a server. The client would be an application such as a Python script or web UI application and the server would be the network device or controller.
In this age of virtualized environments, public and private clouds, APIs are driving the evolution of network management from manual configuration of hardware and software to more automated and scalable techniques.
A majority, if not all of the devices being shipped from leading vendors today come with APIs. Most of the APIs that exist today within network infrastructure are HTTP-based RESTful APIs and the Netconf API.
What is FortiOS?
FortiOS is Fortinet’s network operating system that is the software foundation of Fortigate. It enables the Fortinet Security Fabric, allowing organizations to readily control their security and networking capabilities and achieve a security-driven network with one intuitive operating system. FortiOS activates the Fortinet Security Fabric for enhanced protection from the edge to the cloud.
The FortiGate REST API
Fortigate REST API is a very useful and powerful tool for network developers and programmers. It is directly built into your FortiGate device.
The FortiOS REST API provides configuration and state monitoring programmability options for FortiGate appliances or VMs. This allows for ease of scalability of administrative tasks and the ability to provide rapid response to changes in the environment.
The following types of REST APIs are supported:
- Configuration APIs retrieve and modify CLI configuration items. For example, create or delete a firewall policy; view or change system settings.
- Monitor APIs retrieve dynamic data and perform system/network operations. For example, restart or shut down a FortiGate; backup or restore configuration settings.
In a local network, you can communicate with the FortiOS REST API through your web browser by typing REQUEST into the address bar.
After the request is sent to Fortigate and internally processed, you’ll get a raw result back in JSON format. By adding filtering parameters to the request, a filtered response will be returned.
For convenience, I’ll be using the Try it Out feature of the Fortinet Developer Network. It provides an easy to use interactive interface that allows you to build requests which you can then send to your Fortigate. With FNDN, you can explore the FortiOS REST functionality of your Fortigate, see an immediate response and explore the whole system more efficiently.
In this series of articles and/or YouTube videos, we’ll delve into how one can get started with practically developing customized and relevant programmability solutions for their Fortinet Network Security fabric using Open-source tools e.g Python, Linux, Git, Postman, and Ansible.
You’ll learn about operational scripting, automation and network DevOps pipeline’s integration points on top of your Fortinet security infrastructure. By the end of these series, you’ll be better placed to programmatically monitor, detect and mitigate threats on your network, secure cloud resources with APIs and automate security workflows!
Continue to Part 2 of this series: FortiGate REST API Token Authentication
More Blogs for you:
- Exploring Possibilities in Cybersecurity
- Microsoft Certifications: The What, Where, How and Why
- Top-Rated Network Certifications and Skills
- Best IoT (Internet of Things) training for Beginners
- Network Transformation and Technology Trends for 2020
Relevant Exams: NSE4

 Finland
Finland Germany
Germany Denmark
Denmark Sweden
Sweden Italy
Italy Netherlands
Netherlands Norway
Norway 

































No Comments